Configuring SAML-Based Single Sign-On (SSO) in Microsoft Entra ID
Note: Support for Federated Identity Management (IdM) Authentication to the HP Insights Web Console was introduced in August 2021.
This document provides detailed instructions for configuring Microsoft Entra ID (previously called Azure Active Directory) to support Single Sign-On (SSO).
SAML (Security Assertion Markup Language) is a widely used protocol for enabling secure and seamless authentication. By integrating SAML as an authentication provider, Entra ID allows both system users and end-users to authenticate once and gain access to various HP Insightsapplications. This guide explains the steps required to configure SAML for logging into the Web Console for administrators.
Note: For information on how SSO works with HP Insights. Refer to the Configuring the Single Sign-on (SSO) login to the Web Console Configuring Federated IdM Authentication on the Web Console document.
Step 1: Add HP Insights application in the Microsoft Entra ID web portal
This step provides detailed instructions for creating an application that can be used to enable Single Sign-On (SSO) for the following scenarios:
-
System users logging into the Web Console.
-
End-users logging into applications such as Print Scout and User Portal.
If you are using Microsoft Entra ID as your identity provider, you'll need to create a non-gallery application in Entra AD for use with HP Insights.
Note: You’ll need a Global Administrator account in Azure to add an application in the Azure portal.
-
Sign into the Azure Portal (https://portal.azure.com/).
-
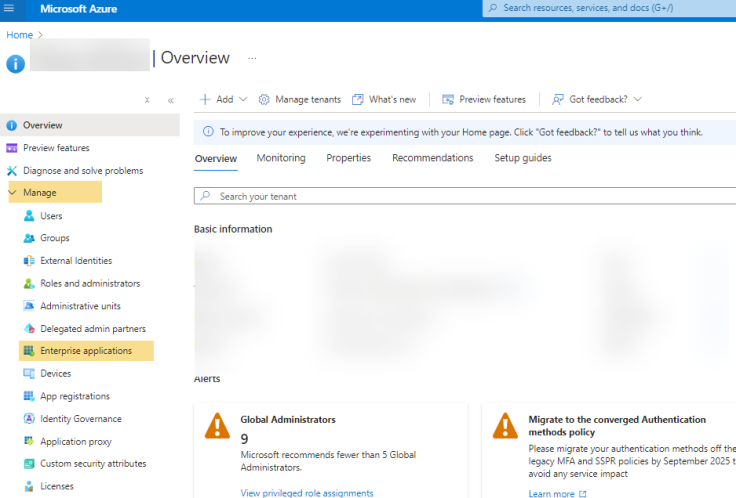
Look for Microsoft Entra ID
- In the left hand menu, select Manage > Enterprise Applications.
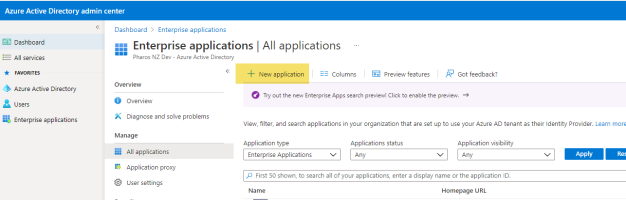
3. Click New Application.
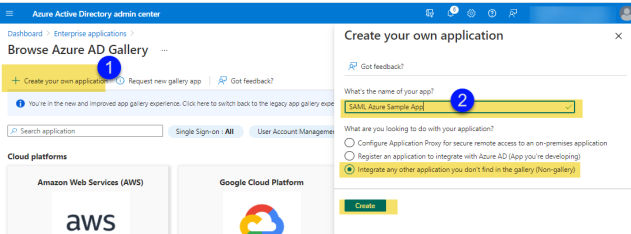
3. Click Create your own application, give the new app a name, select the Non-gallery option as shown below and then click Create. This will add the application to Entra ID.
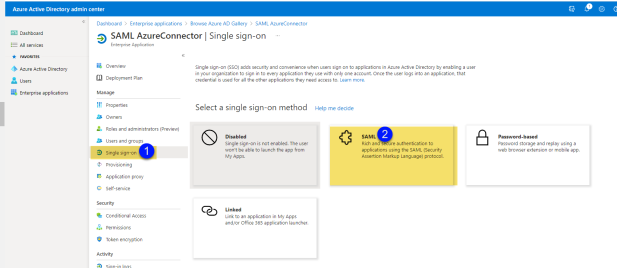
4. In the left-hand menu, select Single Sign-on and then select SAML.
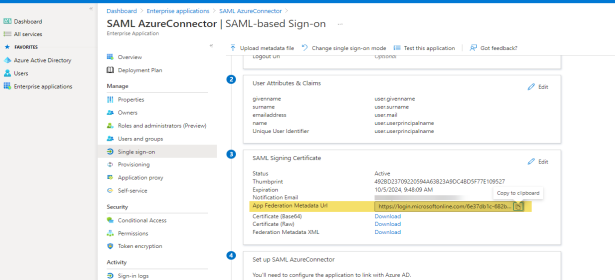
5. In the Setup screen, locate Set up <SAML application name> and copy the values of the following into clipboard. You will need these later when configuring SSO in the HP Insights web console.
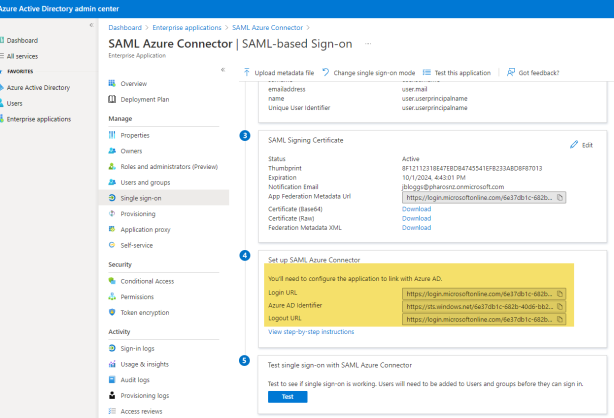
The following table provides a quick reference to help translate HP Insights terminology to the MS Entra ID SAML provider.
|
Secure Print |
Microsoft Entra ID |
|---|---|
| Entity ID |
This is equivalent to Microsoft Entra Identifier in Microsoft Entra ID. Tip: This value typically starts with https://sts.windows.net |
| Single Sign-in URL |
Login URL Tip: Look for /saml2 at the end of the URL |
| Single Sign-out URL | Logout URL
Tip: Look for /saml2 at the end of the URL |
6. Alternatively, you can copy the App Federation Metadata URL, which contains all the information you need to configure SAML in the HP Insights Web Console.
Next Steps
-
To configure SAML SSO for system users to be able to log in to the web console (Legacy SSO for admins), proceed to Step 2: Set up SAML SSO on the HP Insights Web Console instructions below.
-
To configure SAML with SCIM(New SSO for admins) , proceed to Step 2 to Configure SSO with SCIM.
-
To configure SAML SSO for print users, refer to the SAML section in the Authentication Providers document.
For System Users: Completing the SAML SSO configuration system users login to the web console (Legacy SSO only)
Step 2:Set up SAML SSO on the HP Insights Web Console
1. Log in to the HP Insights Web Console.
2. Navigate to the Account Settings > Single Sign-on Configuration tab and select SAML under Provider Types. This opens the SAML SSO Provider Configuration page.
3. Enter the SAML information you have obtained from your identity provider.
|
Field |
Description |
|---|---|
| Entity ID |
This is the unique URL that identifies your Identity Provider. This is sometimes referred to as the Issuer. Tip: In MS Entra ID , this is called Microsoft Entra Identifier. |
| Single Sign-in URL |
The URL on your identity provider's server where HP Insights redirects users for signing in. Tip: In MS Entra ID , this is called Login URL. |
| Signing Certificate |
The X.509 certificate issued by your identity provider. This certificate is used to validate the signature of the requests from the identity provider to HP Insights. Tip: In MS Entra ID , you can find the signing certificate in the element called X509Certificate. |
| Single Sign-out URL |
(Optional) This is the URL where users are redirected when logging out from the HP Insights web console.
Tip: In MS Entra ID , this is called Logout URL |
| Email Attribute Name |
This is the attribute that HP Insights uses to get the user's email address. System users in HP Insights are created using the email address that corresponds with their SAML email address. The default value is http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress. |
| Sign Authentication Request |
This setting determines whether the initial user sign in request to the identity provider is signed by HP Insights or not. If it's set to No, anyone can initialize authentication request to the identity provider. The default value for this setting is Yes. |
Step 3: Add HP Insights information in the Identity Provider
The identity provider requires information from HP Insights to establish transfer of information between HP Insights and the identity provider.
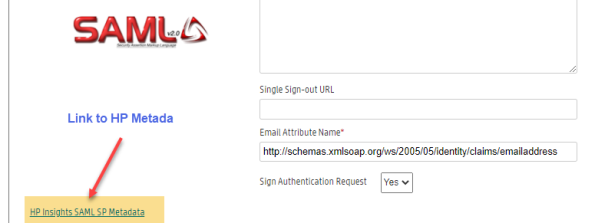
a. Obtain information from metadata in the HP Insights web console
- Log in to the HP Insights web console and navigate to the Account Settings > Single Sign-on Configuration tab.
- Click the HP Insights SAML SP Metadata link found on the lower left hand side of the SSO Provider Configuration page. This file includes most of the HP Insights information required by the identity provider such as certificate, the entity ID, the Assertion Consumer Service URL, etc.
b. Add information from metadata into your identity provider
On your identity provider's configuration panel, copy and paste the following information into your identity provider's configuration interface.
|
Field |
Description |
Microsoft Entra ID |
|---|---|---|
| Assertion Consumer Service(ACS) URL or Callback URL |
The URL where the SAML assertion is sent after the identity provider has authenticated the user. Tip: Search for Location under Assertion ConsumerService in the metadata. Examples:
|
In Microsoft Entra ID , this is known as Reply URL (Assertion Consumer Service URL). |
| Entity ID |
This is the unique identifier for HP Insights. It is used by the identity provider to identify which service made the request. Tip: Look for the value of the entityID parameter within the metadata. |
In Microsoft Entra ID, this is called Identifier (Entity ID). |
| X509Certificate |
The public X.509 certificate of HP Insights. Used to generate fingerprint to validate SAML responses. Tip: Look for the value of X509Certificate within the metadata. |
Step 4: Assign users and groups to the HP Insights application
Assign the users and groups that will log in to the HP Insights Web console usingMicrosoft Entra ID as the identity provider:
-
In the HP Insights application you created in Microsoft Entra ID, click Users and groups.
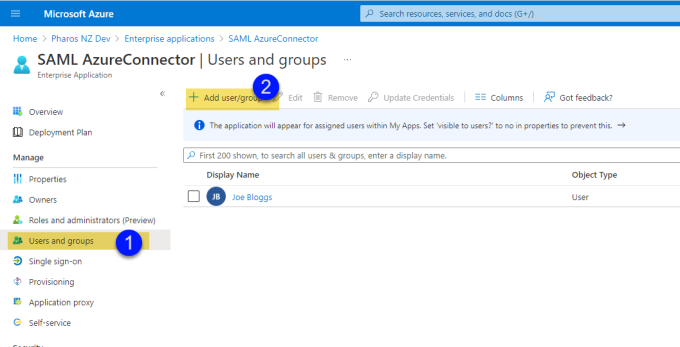
-
Click Add user/groups.
-
Select the appropriate users and groups. Click None Selected to open up a list of users and then select the users you want to add.
-
Click Assign to assign the selected users/groups to the HP Insights application within Microsoft Entra ID.
Note: Make sure that the user account has an email address in the Microsoft Entra ID. This should exactly match the email address that you add to the HP Insights web console.
Step 5: Create an External User
- Select Users > System Users.
- Click the Create button. This opens the Create System User dialog.
- Enter the following required fields: Name, Email Address, Role Name, and access group. The Email address must match their primary email address in the identity provider.
- Select Save when you are done.
- A new user will be added to the System Users list.
After creating a user, the next step is to invite the user to the HP Insights system. Newly created users will not be able to login to the HP Insights system until they are invited.
Step 6: Invite an External User
- Select Users > System Users.
- Select the user(s) you want to invite by clicking on the checkbox next to their name(s). You can invite multiple users by checking multiple user names.
- Click the Invite button. This opens the Invite System Users dialog box. It will show a message letting you know how many people will be invited to use HP Insights.
- Click the Send button. The selected users will receive an email message to login to HP Insights. The email message will contain a link to access HP Insights.
For End Users: Configuring SAML SSO for HP Insights Applications
To configure SAML SSO for end-users, refer to the separate document titled User Authentication Providers. Locate the SAML section and follow the instructions outlined in the document.